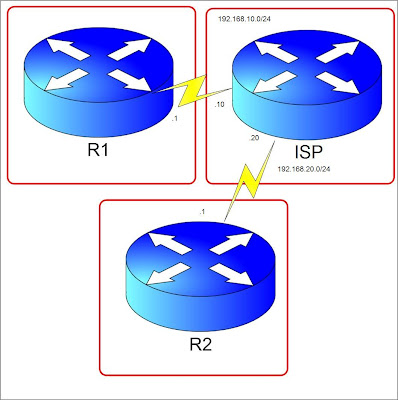
Let's pretend ISP is the Internet Cloud. We have R1 and R2 connected through an internet leased line to their ISP's. Lets say R2 has a server 2.2.2.2 which R1 needs to access from 1.1.1.1 in its network. (1.1.1.1 and 2.2.2.2 are just loopback addresses in R1 and R2 respectively) We will build a VPN tunnel allowing 1.1.1.1 to access 2.2.2.2 and vice versa. Steps are numbered but not necessarily the standard way but a more favorable way of configuring.
1. Create an access-list on both R1 and R2. This will indicate the "interesting traffic". This means that anything that matches the ACL applied to the tunnel configuration will pass through the tunnel instead of exiting the interface facing the internet.
R1(config)#access-list 100 permit ip host 1.1.1.1 host 2.2.2.2
R2(config)#access-list 100 permit ip host 2.2.2.2 host 1.1.1.1
Notice that the ACL's mirror each other.
2. Configure an ISAKMP key. This key will be used to generate more keys for VPN tunnel creation and must match between the peers.
R1(config)#crypto isakmp key 0 myvpnrouter address 192.168.20.1
R2(config)#crypto isakmp key 0 myvpnrouter address 192.168.10.1
The ip address at the end of the command is the IP address of the peer router.
3. Create an ISAKMP policy. The policy components like hashing, authentication, Diffie-Helman group, and lifetime must match. You can configure many different policies and the routers will check the ISAKMP policy until it finds a match of its own. It is checked sequentially by using policy sequence numbers. ISAKMP negotiation is also called Phase 1.
R1(config-isakmp)#crypto isakmp policy 10
R1(config-isakmp)#group 2
R1(config-isakmp)#hash md5
R1(config-isakmp)#lifetime 28800
R1(config-isakmp)#encryption aes
R1(config-isakmp)#authentication pre-share
R2(config-isakmp)#crypto isakmp policy 10
R2(config-isakmp)#group 2
R2(config-isakmp)#hash md5
R2(config-isakmp)#lifetime 28800
R2(config-isakmp)#encryption aes
R2(config-isakmp)#authentication pre-share
4. Configure Phase 2 which are IPSEC parameters.
R1(config)#crypto ipsec transform-set TRANSFORMERS esp-3des esp-sha-hmac
R1(config)#crypto ipsec security-association lifetime seconds 28800
R2(config)#crypto ipsec transform-set TRANSFORMERS esp-3des esp-sha-hmac
R2(config)#crypto ipsec security-association lifetime seconds 28800
Configure a crypto map.
R1(config)#crypto map MYMAP 10 ipsec-isakmp
% NOTE: This new crypto map will remain disabled until a peer
and a valid access list have been configured.
R1(config-crypto-map)#match address 100
R1(config-crypto-map)#description to R2
R1(config-crypto-map)#set transform-set TRANSFORMERS
R1(config-crypto-map)#set peer 192.168.20.1
R1(config-crypto-map)#set security-association lifetime seconds 28800
R2(config)#crypto map MYMAP 10 ipsec-isakmp
% NOTE: This new crypto map will remain disabled until a peer
and a valid access list have been configured.
R2(config-crypto-map)#match address 100
R2(config-crypto-map)#description to R1
R2(config-crypto-map)#set transform-set TRANSFORMERS
R2(config-crypto-map)#set peer 192.168.10.1
R2(config-crypto-map)#set security-association lifetime seconds 28800
5. Apply the Crypto map to the outgoing interface.
R1(config)#int se1/1
R1(config-if)#crypto map MYMAP
R1(config-if)#
*Jul 11 13:05:47.007: %CRYPTO-6-ISAKMP_ON_OFF: ISAKMP is ON
R2(config)#int se1/2
R2(config-if)#crypto map MYMAP
R2(config-if)#
*Jul 11 13:05:47.007: %CRYPTO-6-ISAKMP_ON_OFF: ISAKMP is ON
6. Make sure you have a route towards the peer vpn router public ip. In our case lets create a default route.
R1(config)#ip route 0.0.0.0 0.0.0.0 192.168.10.10 name To_R2
R2(config)#ip route 0.0.0.0 0.0.0.0 192.168.20.20 name To_R1
7. Finally lets test the connection. The tunnel won't come up until there is interesting traffic passing through the tunnel. Any traffic that will hit the access-list we matched in the crypto-map will trigger the tunnel negotiation. In our case lets ping 2.2.2.2 from R1 sourcing from the Loopback interface 1.1.1.1. In the ISP router, I have configured a route for the 2 loopback addresses.
ISP(config)#ip route 2.2.2.2 255.255.255.255 192.168.20.1
ISP(config)#ip route 1.1.1.1 255.255.255.255 192.168.10.1
R1#ping 2.2.2.2 source 1.1.1.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 2.2.2.2, timeout is 2 seconds:
Packet sent with a source address of 1.1.1.1
!!!!!
To verify if the tunnel is up and running, lets use the "show crypto isakmp sa" to check Phase 1 status.
R1#sh cry isakmp sa
dst src state conn-id slot status
192.168.20.1 192.168.10.1 QM_IDLE 1 0 ACTIVE
QM_IDLE means that the tunnel is up. If the state is not that, that means that there is a problem.
"Show crypto ipsec sa" displays Phase 2 information which includes the number of packets that used the tunnel and the source and destination IP. Thats it for the configuration. For more detailed information on the VPN negotiation process visit this link. Cheers




thank you so much CiscoDreamer.
Very good tutorial for me.
Have a nice day,
aby